Many consumers and business are anxious about the security of their information, both on their own devices and on business networks. While they worry about being hacked, they continue to engage in risky activities. According to a recent survey published by Arbor Networks, 75% of adults say they are concerned about their security, privacy, malware and websites tracking them, but they don’t take any action to protect themselves.
Many consumers and business are anxious about the security of their information, both on their own devices and on business networks. While they worry about being hacked, they continue to engage in risky activities. According to a recent survey published by Arbor Networks, 75% of adults say they are concerned about their security, privacy, malware and websites tracking them, but they don’t take any action to protect themselves.
As a result, damage from emotional distress caused by anxiety occurs even before any hacking takes place. Part of the problem seems to be that consumers don’t know what to do when they are hacked and don’t know how to avoid being a target. They describe themselves as being “tech-savvy” but don’t take measures to protect their data. To counteract the anxiety requires a solution that ensures data protection even in the face of hacking activity.
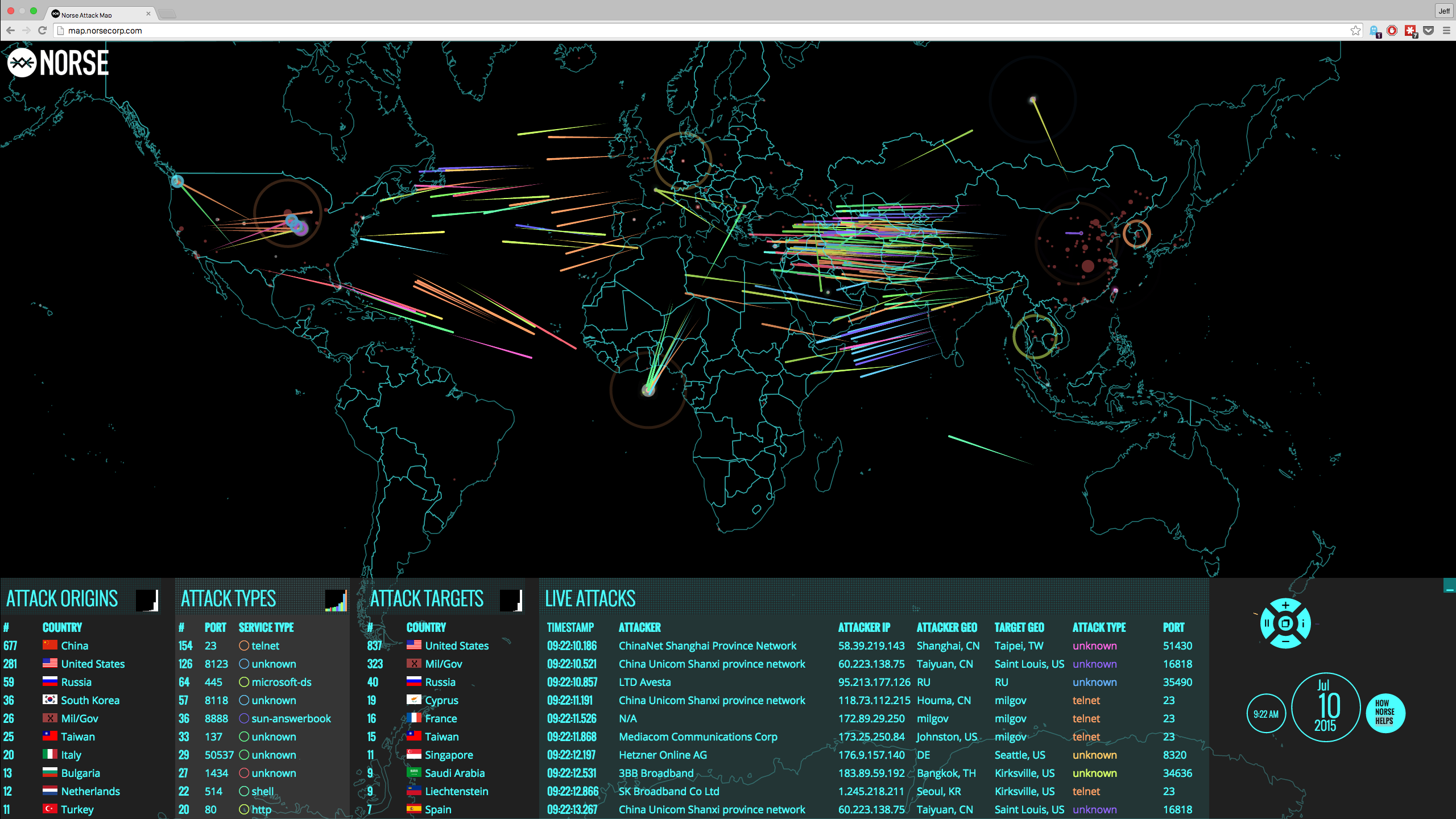
Cybersecurity Risks
The risks you face as a consumer include the theft of personally identifiable information, the theft of login credentials and identity theft. Most hacking efforts focus on passwords as the critical weak point in IT systems. The Federal Trade Commission gives details of various risks and countermeasures. Many consumers are not careful with their sensitive data and place it on social networks and in the cloud without the proper protection. As a result, whenever cases of hacking hit the news, they become more and more anxious about the safety of their personal information.
In addition to sensitive information such as passwords and credit card numbers, you may not want information about yourself to be gathered without your permission. Many consumers attach value to data such as purchase history, locations, and personal preferences and want to keep control of this information. When your emails, files stored in the cloud and online orders are mined for creating consumer profiles, you may wonder whether the information is, in fact, correct and what third parties might do with it.
Finally, consumers worry about sensitive health, financial and legal information falling into the wrong hands. You don’t want to be denied health insurance because you looked up certain symptoms online or lose a job opportunity because confidential legal information leaked out. You probably want your personal financial situation to remain private and don’t want personal concerns or plans to be part of a semi-public profile.
When you send unencrypted email, use mobile apps, post on social networks and store files and pictures online, this information is often available to third parties and recorded. Records such as these can be consolidated and used to assemble detailed consumer profiles that have value. If you don’t want your personal data collected and sold, you have to take measures to reduce online access to your information.
All these risks are associated with different levels of potential damages. Where identity theft can cause significant financial losses, the creation of inaccurate profiles or the leakage of confidential data can also affect your lifestyle, job prospects or career. People who are concerned about cybersecurity and want to protect their personal data have to take measures to keep their information safe.
Effective Data Protection
There are a number of things you can do to reduce the risk to your data and increase your cybersecurity. Basically you want to prevent theft of your passwords, keep your confidential information safe and increase the level of protection for your sensitive data. The University of California details some strategies to avoid being hacked. When you take a few critical measures to reduce your risks, your level of anxiety about hacking will decrease.
The first thing you can do is change your passwords to something that is hard to guess and make sure you have different passwords for different accounts and purposes. A good trick for coming up with secure passwords that you can remember is to base them on a phrase, such as a rhyme or a line from a song, and use the first letters, or last letters of the words. Throw in a character such as a bracket or exclamation point at the beginning or end and you have a secure password.
A second factor in cybersecurity is to develop a healthy scepticism of links in emails. Even when the email seems to come from someone you know, your acquaintance’s email account could have been hacked and the link could be malicious. When you’re not expecting a link, question whether it is valid.
A third strategy is to keep your computers and devices updated and stripped down to what you really need and use. Keep only programs and apps that deliver something or some function that you can’t get otherwise and regularly delete software you no longer use.
Finally, you have to keep sensitive data safe. When you store files, photographs or information online or when you email sensitive information, encrypt it. Not all encryption is equally secure. For example, if you can log into your email account from a computer other than your own and read your email and files, any hacker with your password could do the same. You need data-centric encryption that has separate keys that you control.
This sounds difficult but new technology can make it completely transparent. It can be as easy as downloading a browser plug-in that masks your data and prevents unauthorized parties from reading it. You control the keys and only people who you specifically authorize to read your data can see the clear text. You can even select what parts of the information you want masked to keep the confidential parts of your data safe.
When you take such measures to improve your cybersecurity, you become less of a target for data breaches. You can read about hackers and how they cracked their target’s passwords or how they accessed files they stored in the cloud or sent via email. If you have taken the described measures to protect your data you can say to yourself that you are less at risk. Cybersecurity anxiety will be for others while you know your own data to be safe.

With CloudMask, only your authorized parties can decrypt and see your data. Not hackers with your valid password, Not Cloud Providers, Not Government Agencies, and Not even CloudMask can see your protected data. Twenty-six government cybersecurity agencies around the world back these claims.
Watch our video and demo at www.vimeo.com/cloudmask
Share this article: