This article is the third in a series that discusses data breach threats and possible solutions. The first two articles, “What You Need to Know,” and “Threats and Consequences,” make it clear that businesses need to take action to reduce data breach risks. The current article presents encryption as a possible solution but details what type of encryption is needed to effectively address data breach issues.
What is Encryption and What are the Challenges?
Encryption is a process that uses an algorithm to transform data into a form in which there is a low probability of assigning meaning without the use of a confidential key. Accordingly, encryption is composed of two major components: the algorithm and the key.
Encryption of sensitive data can be an effective way for a business to reduce its data breach risks. Encryption can be a “safe harbour,” that can limit your exposure to breach notification laws when unauthorized individuals gain access to your data.
But not all types of encryption are equally effective. To understand the how to select the right encryption solution, lets look to the NIST recommendations in relation to the above two factors, algorithm and keys
- The use of the Federal Information Processing Standard (FIPS) approved algorithm
- The management and control of the decryption keys by the end user
Ease of use is another consideration. If the encryption application is difficult to use or takes a lot of extra time and effort, your employees and partners may try to avoid using it. Many commonly available types of encryption have serious problems.
Cloud Encryption
Cloud service providers can offer “secure” cloud services where they encrypt all traffic to and from the cloud and they may encrypt data even when it is stored, at rest, in the cloud.
The four problems with cloud encryption are:
- · You don’t manage and control the encryption keys
- · Cloud service provider connected apps (e.g.. through API) and personnel may have access to your data
- · The data is in clear text during data processing (it is decrypted before processing it)
- · The encrypted data can’t be searched or processed
If you don’t control the keys, you’ll never have control on your data security. Then you suffer the consequences even if it was not directly your mistake.
Encrypted data in the cloud must be decrypted before processing by the cloud application. This will create another risk. As an example, when you are using Gmail and your data is encrypted during transmission and in storage, the data is decrypted when it moves to the Gmail server to be accessed by you. This same data will be accessed by a hacker who hacks your password.
Local Encryption
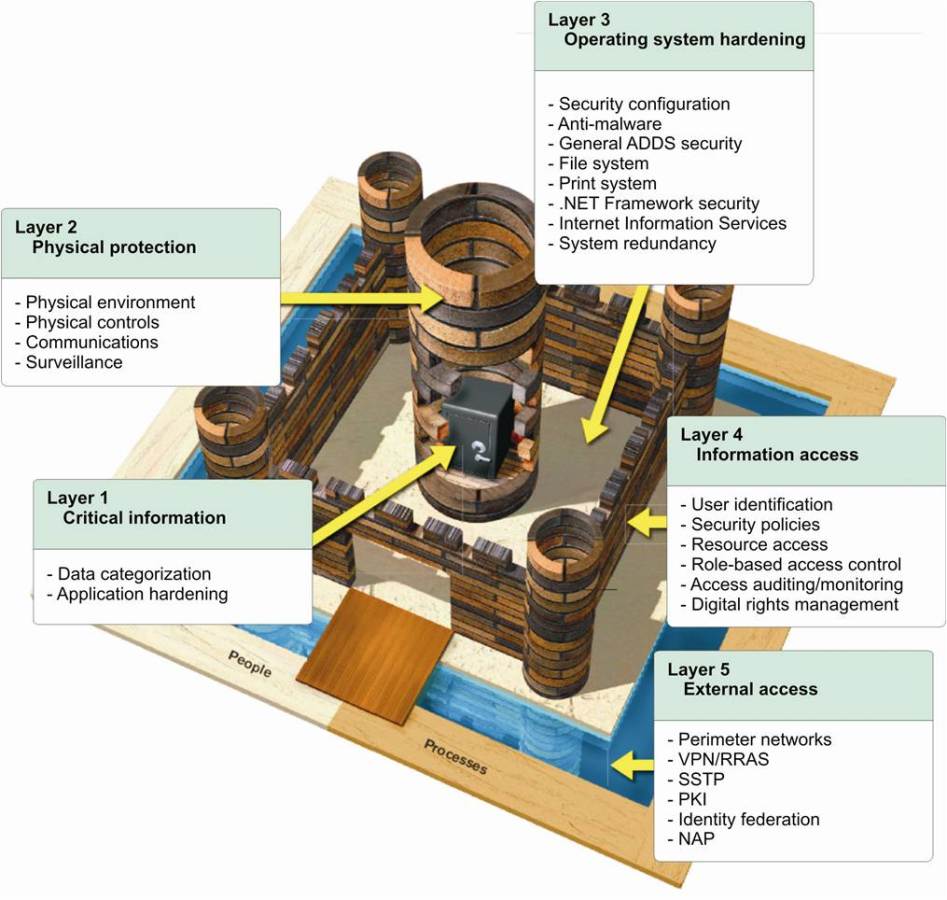
Many businesses realize that cloud encryption may not provide the level of data security that they need so they keep the data on their own servers. This strategy is flawed because your local system is probably less secure than the cloud. The perimeter security typically used on a company’s IT system is no longer enough to keep data secure. Just as with the cloud, you can add encryption to increase security but you have to choose the right type of encryption.
Some applications offer complete disk or file encryption but you can run into problems with ease of use and identification. The encrypted data has to be decrypted each time anyone wants to search it or carry out an operation. The data will be in clear and vulnerable on the network during any use of the data. Your system typically relies on user names and passwords to identify employees or other authorized personnel. This means anyone who has stolen or been given a valid user name and password can log into your system and masquerade as an employee, often from anywhere in the world. Encrypting your data this way instead of in the cloud is not an effective solution.
Encrypting Communications
Cloud, disk and file encryption deal with data that is either being stored or in transit to and from a storage device. Business is more and more about exchanging data and collaborating. Sensitive data has to be communicated securely among employees, contractors, partners and customers.
A white paper published at MimeCast looks at content encryption with specific references to email. Here the issues with secure encryption are compounded by the fact that you don’t know the security status of many of the endpoints of your communications. If you send sensitive data to a consultant for analysis and your system is perfectly secured, he might be sitting in a coffee shop looking at his email on an unsecured laptop. The communication will be in plain text before it reaches the consultant and a data breach can result.
The Encryption You Need
When you implement the right kind of encryption, it addresses all these issues and allows you and your collaborators to work with sensitive data securely, confident that your data will not be exposed in a data breach. The characteristics needed in such an application are the following:
Data-centric encryption. You decide what data is sensitive and what data to encrypt.
- End-to-end encryption. Your data is encrypted when it leaves your computer or mobile device and stays encrypted until it is used.
- Control of keys. Keys are stored on your computer or device and on those of the people you authorize to see your data.
- Third party certification (FIPS and others). Independent experts have evaluated the encryption used and have certified it as secure.
- Ease of use. The encryption application functions in a completely transparent way for the user and does not require complicated additional steps or training.
The CloudMask Solution
CloudMask offers an encryption solution that satisfies data-centric encryption requirements. The CloudMask application avoids the pitfalls of cloud, disk or file encryption and gives you complete, secure control of your data. Only the people you authorize can read your data and only you and the authorized individuals have the encryption keys.
With CloudMask, you download a browser plug-in and you are set to encrypt your data. You can decide which data to encrypt and that data leaves your computer or mobile device as an unintelligible series of characters. Nobody, not hackers, not third parties like Google, not IT administrators or tech support can read what you have encrypted. CloudMask is Common Criteria certified as secure and the encryption can’t be broken by unauthorized parties. Your data is safe until it is used.
When you authorize another individual to read your data, they can look at what you sent them. The process is transparent and easy to use. The protection is real end-to-end encryption, from the time you create the information to the time it is read by your authorized partner. You have complete control, independently of any other security measures your company might want to take.
With CloudMask, you can maintain your normal cloud security, your standard company IT network security and your email account protections. CloudMask represents an additional secure layer that reduces the overall risks of a data breach for your data. When your other protections fail, CloudMask prevents unauthorized individuals from reading your data. Your company’s exposure to data breach risks is diminished to acceptable levels and your data will remain safe.

With CloudMask, only your authorized parties can decrypt and see your data. Not hackers with your valid password, Not Cloud Providers, Not Government Agencies, and Not even CloudMask can see your protected data. Twenty-six government cybersecurity agencies around the world back these claims.
Watch our video and demo at www.vimeo.com/cloudmask
Share this article: