The assumption that software security can stay ahead of the hackers is not true because the software security industry is always reacting to threats that hackers expose. Once hackers start exploiting a flaw in an application, security companies try to block the resulting threat by providing security updates for existing software or by developing new programs. Either way, hackers will be one step ahead because the software security industry can’t predict what new threats the hackers will unleash.
Experts On “Staying Ahead of the Hackers”
If you search Google for the phrase, “staying one step ahead of the hackers,” you will find links to expert advice from companies active in software security.
IBM - Staying one step ahead of hackers
IBM makes the following recommendations: “First of all, perform a gap analysis. Invite our professional services and ask us to come and perform a vulnerability assessment on [your] public Web sites and internally. Second, deploy security controls and measures within the organization to understand exactly what kind of vulnerabilities you have. Deploy, as fast as possible, our intelligence platform. It’s going to give all the information that is needed to mitigate and understand what kind of security risk you hold today and to help you prepare for future attacks.”
Future of Tech - Staying one step ahead of the hackers
The conclusion of this article is: “Every business should have a robust incident response plan and test it regularly. Consumer confidence and the share price can fall if a breach is handled badly. There are massive skill gaps in the cyber security industry so it is good to see more universities offering relevant courses and companies offering apprenticeships to increase expertise.”
Trustwave - How to Stay One Step Ahead of Retail Hackers
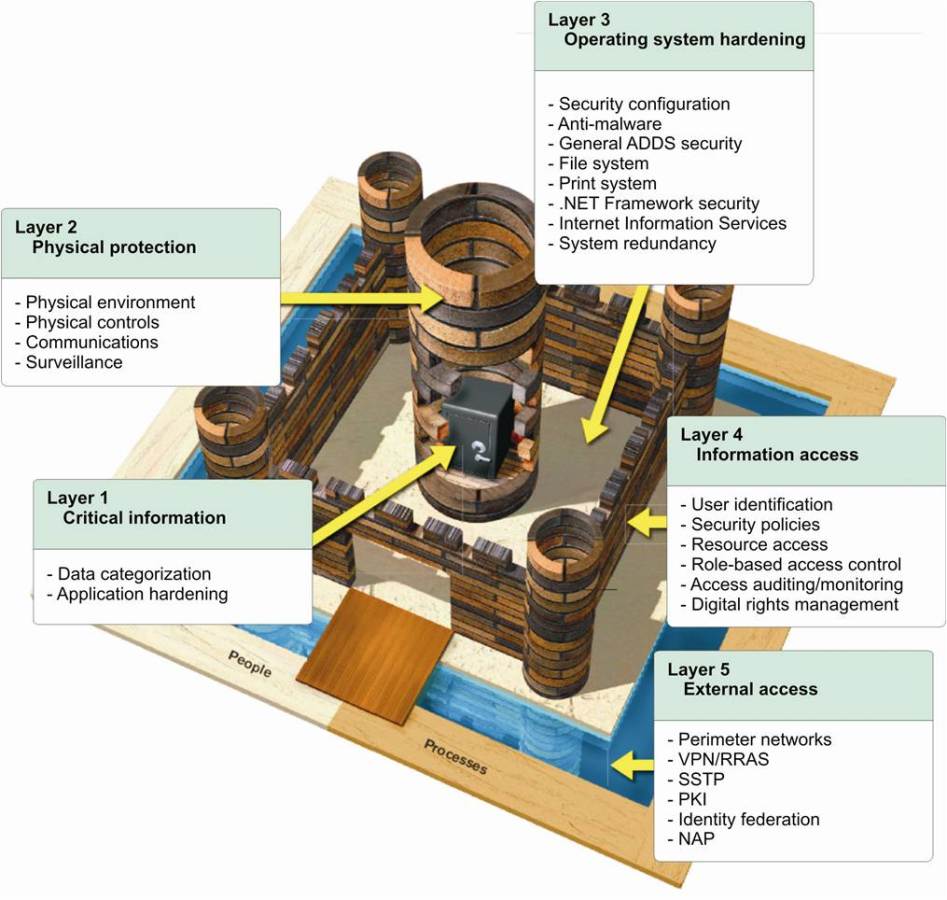
Here the recommendations are: “Look For Vulnerabilities Like a Hacker Would ….. Adopt a Multi-Layered Defense Strategy …. Remember, knowledge is power. The intelligence exists to outsmart the hackers over and over again, and the good guys can, and do, win.”
Latest Cyber Tends: How to Keep One Step Ahead of the Hackers
The closing paragraph is: “Technology cannot keep up with the cyber crime trends. So, it’s up to people to keep an eye on them so they don’t take advantage of us. Stay alert, take time to read popup dialogues, don’t panic, update your software AND hardware, and don’t get your apps from anywhere other than their official stores.“
All of these recommendations and the many YouTube videos that recommend similar approaches are valid for reducing the risk of hacking but they do not keep you one step ahead of the hackers!
Why You Can’t Stay One Step Ahead of Hackers
The reality is that it’s the hackers who are ahead.
If the government and large organizations with million of dollars spent on cybersecurity cannot stay one step ahead of hackers, how can experts recommend this approach to other smaller organizations? It makes no sense.
The cybersecurity industry opinion reflects reality. During the RSA 2015, RSA President Amit Yoran in his keynote address described “Escaping Security’s Dark Ages,” and stated, “We are living in the Dark Ages of security. We cling to outmoded world views and rely on tools and tactics from the past, and yet we are surprised to find ourselves living in an era of chaos and violence.”
Bruce Schneier, one of the leading experts in cybersecurity and encryption, states, “On the Internet, attack is easier than defence. There are a bunch of reasons for this, but primarily it's 1) the complexity of modern networked computer systems and 2) the attacker's ability to choose the time and method of the attack versus the defender's necessity to secure against every type of attack.”
Cornell University published a study titled “What Is the Cyber Offense-Defense Balance?” It stated, “In cyberspace, the offense has the upper hand.” These words, written in 2010 by Deputy Secretary of Defense William Lynn, reflect conventional wisdom among military officers, policymakers, and scholars.”
This clear conflict of reality versus common practice is telling us that Traditional Security has hit its Limits and that we need a New Security Paradigm
The Real Challenges for Cybersecurity
Businesses face risk every day. It’s a part of getting business done, especially in our digital world. Managing risk is critical, and that process starts with a risk assessment. If you don’t assess your risks, they cannot be properly managed and your business is left exposed to threats. A successful risk assessment process aligns with your business goals and helps you reduce risks in a cost-effective way.
In a world with a fast changing business environment with regulations, competition, new applications, new devices etc., how can any business assess risks effectively? How can they protect themselves in an environment where their adversaries are much stronger than they are in technical resources, funds, and time? How can they protect themselves where their adversaries, not only the bad guys but also their own government, their “trusted” service providers and even their own employees become a source of risk?
The Solution – Don’t Trust Anyone
The solution is to not trust others to keep your data safe but to take control of your data security yourself. Low cost, simple-to-install and operate data masking solutions such as CloudMask protect your data from anyone not authorized to view it by you personally. Your data is masked and illegible from the moment you create it on your device to the moment someone you authorize unmasks it and reads it. Nobody else can see your data, not your service providers, the government or even your own in house IT specialists. You retain full control of all your data and when hackers breach your perimeter defences, your data remains safe. You are not only one step ahead of the hackers – you no longer have to worry about them at all.
Please read The Encryption That Businesses Need, But CISOs Forget About

With CloudMask, only your authorized parties can decrypt and see your data. Not hackers with your valid password, Not Cloud Providers, Not Government Agencies, and Not even CloudMask can see your protected data. Twenty-six government cybersecurity agencies around the world back these claims.
Watch our video and demo at www.vimeo.com/cloudmask
Share this article: