Encryption is necessary after all, so the only discussions about this technology and these services should be about choosing a solution. When to comes to truly protecting data, encryption is a no-brainer. In fact, some industry regulations require that businesses and associations encrypt specific information. Health care is a great example of this, but organizations in...
The assumption that software security can stay ahead of the hackers is not true because the software security industry is always reacting to threats that hackers expose. Once hackers start exploiting a flaw in an application, security companies try to block the resulting threat by providing security updates for existing software or by developing new programs. Either...
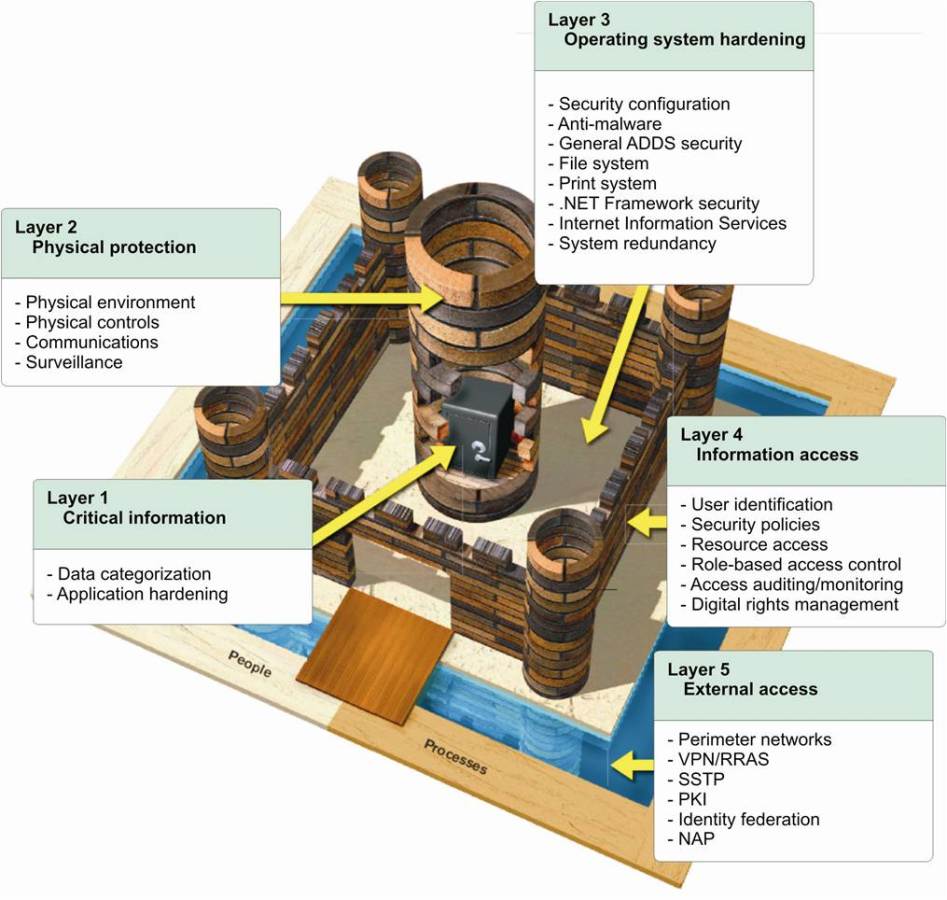
By Joseph Steinberg CEO, SecureMySocial @JosephSteinberg For many years, information security professionals have discussed, and promoted, a strategy known as “Defense In Depth,” in which an organization utilizes multiple layers of security controls rather than just one layer, with the hope that if some vulnerability exists in one of the layers, the...
Data security and privacy compliance and competitiveness are one in the same for law firms. For better or worse, whether lawyers love it or hate it, technology is now a fundamental aspect of the legal sector. While the reliance on IT isn't new in law by any means, modern technologies such as cloud computing, mobile devices, and software-as-a-service solutions now play...
Federal governments and major technology firms are arguing for or against encryption, respectively. But why? Due to recent political turmoil and devastating events overseas, the topic of end-to-end encryption has reentered public discussion. At the center of the debate, you have federal governments and major technology firms, each arguing for or against encryption. The...
By Joseph Steinberg CEO, SecureMySocial @JosephSteinberg Many businesspeople put their firms’ data at risk because they fail to understand several important concepts about encryption. Simply understanding that data can be protected from unauthorized parties by encrypting it is insufficient to deliver security; in order to secure information people must know when...
Data Masking/Tokenization/Anonymization replaces sensitive information with fictitious data while retaining the original data format. The data masking process lets you continue to work with your data as if it were not encrypted. Databases, business applications and collaboration software continue to work as if the data was real, but unauthorized personnel only have...
September 19, 2017
Leave a comment
Compliance,
Data Masking,
data residency,
Tokenization
By Wael Aggan
Jurisdictions around the world, including the European Union and Canada, are enacting laws and creating regulations forcing companies that collect personally identifiable information (PII) to store the data of their residents within their national boundaries. This concept is known as data residency and the idea is that local privacy laws will apply to data stored...
August 27, 2017
Leave a comment
Personal Data Protection,
Data Sovereignty,
data residency
By Wael Aggan
Email is one of the most critical business tools and a major component of the lives of many people. At the same time, it seems to lack adequate security as the Clinton campaign email leaks and the publication of France’s Macron emails have shown. Email is at the same time insecure but used to share important and often sensitive information. While companies encrypt...
The ITAR (International Traffic in Arms Regulations) legislation details what measures businesses and individuals must take to comply with ITAR requirements and specifies severe penalties, both civil and criminal, for non-compliance. The reach of the regulations is broad and suppliers of all kinds may be subject to requirements to keep sensitive information secure and...