WHY CLOUDMASK?
Cross-Organizational Boundaries
Avoid limiting yourself to specific Cloud vendors. CloudMask protects your data across organizational and application boundaries.
You can leverage the full potential of Cloud ecosystem with its many providers, software developers and ongoing innovations.
Develop With Your Preferred Cloud
Build hybrid applications using the Cloud platform that best fits your needs.
Your data remains protected as it is processed on the Cloud and is only decrypted once it reaches your trusted on-premise server.
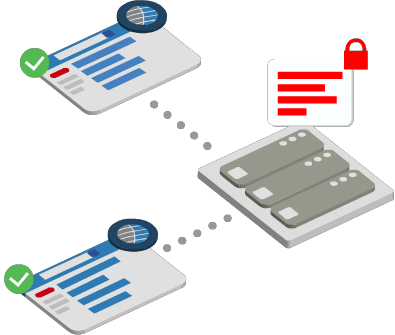
Mitigate Insider Threat
Strengthen your on-premise security by ensuring that administrators, root users and other insiders do not have implicit data access. Data remains protected in-use while being processed in server memory.
Even CloudMask system administrator can only access the data if they possess keys that have been explicitly authorized.
Comply With Privacy Regulations
Apply Privacy By Design and Privacy By Default throughout your on-premise and cloud environments. Use fine-grained policies to centrally manage access based on user, application context, and fields in question.
Grant access when a valid reason exists and for only as long as required. When regulations change, propagate the change with a single click.
Easier Than You Think
All you need for integrated & efficient key management
Hold Your Own Key
Each user/service device has its own encryption key under its sole control. It is never shared nor transmitted over the network.HSM & HW Tokens
Use your preferred cryptographic engine along with integrated HSM and Hardware Token support.Multi-Device Trust
Enable users to authorize keys for each of their devices without administrative overhead.Key Management
Use a combination of internal PKI, public CA, and/or our securely generated keys.Identity Providers
Automatically generate keys using private and public Identity Providers with OpenID and SAML standards.Assurance Levels
Assign different levels based on how keys have been activated. Elevate the level through peer-to-peer trust or officer approval.Temporal Access
Grant field-specific access to desired entities. Revoke keys manually or automatically after a set period of time.Organizational Keys
Ensure that data is automatically encrypted for applicable organizational keys for the purpose of recovery, auditing and forensics.Segregate Encrypted Data
Send a one-way token to the application and store your encrypted data separately on-premise or on Cloud.MANAGE AT SCALE
Distributed Workload
All cryptographic operations are done on end-point devices. As more users are activated, CloudMask leverages their devices' processing power.
There are no encryption servers or gateways that can introduce a bottleneck.
Evolving Encryption
As guidelines evolve, data needs to be re-encrypted using stronger algorithms.
CloudMask lets you distribute the re-encryption workload among available trusted devices, without impacting your application.
Change Management
Each data element is tagged with its associated policy at the moment of its creation and throughout its lifecycle.
When policies change, it is immediately applied without the need to read or write data to the applications.
Auditing & Monitoring
Every data and key operation is securely logged. Monitor files and fields access inside and outside your organization.
Block abnormal access patterns based on parameters such as frequency, location and device. For more insight, feed the trace to your SIEM system.
