The application of best practices to a business process can give you the results you want. For example, quality assurance best practices result in the specified level of product quality and best practices in manufacturing reduce the number of product defects. Applied to data security, best practices can keep the data on your computer and mobile devices safe as long as it stays there!
The application of best practices to a business process can give you the results you want. For example, quality assurance best practices result in the specified level of product quality and best practices in manufacturing reduce the number of product defects. Applied to data security, best practices can keep the data on your computer and mobile devices safe as long as it stays there!
In today’s collaborative business environment such a limitation is not viable. You have to constantly exchange information with partners, customers, suppliers and government agencies. Your sensitive data leaves your computer or mobile device for those of your partners where you do not have any idea regarding their security practices or how they secure their information. Your data leaves your system for an environment you do not control and about which you often know very little. You need a new solution that allows you to control your data even when it is outside the security environment you control.
Typical Security Best Practices and Their Limitations
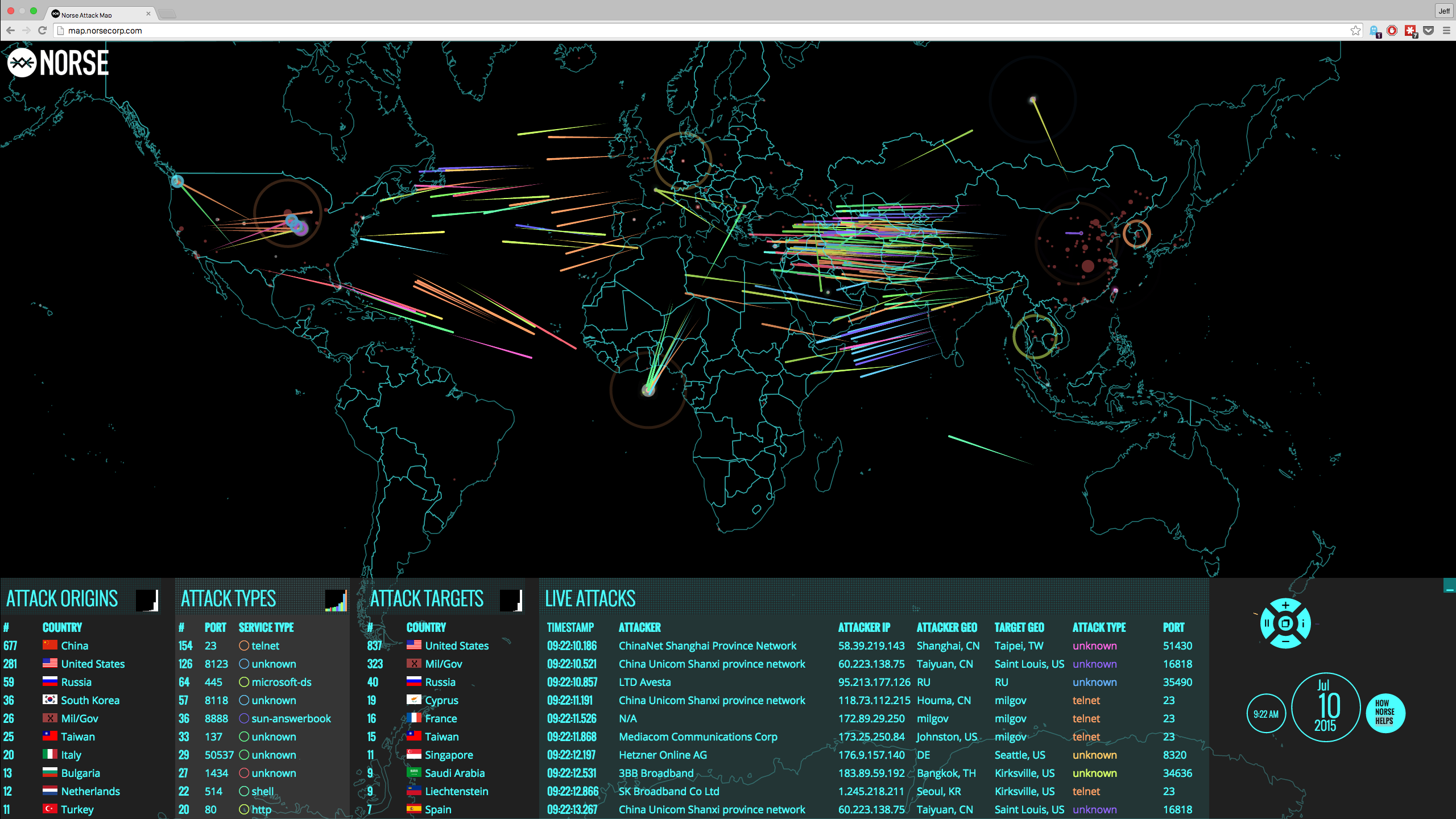
When you use email, file sharing or SaaS applications, your data moves between numerous service providers around the world before it reaches its destination. The security of those providers and that of your recipients is not of equal strength.
"You can strengthen the links of the chain that you control, but you do not know what measures your collaborators have taken at their end. As we all know, “the chain is only as strong as its weakest link, ” and there always be weak links somewhere along the way."
For example, Google details some best practices to secure data in their G Suite. Google recommends that you activate two-factor authorization, applying and enforcing the use of strong passwords, take anti-spoofing measures, and monitoring user behavior for security policy breaches.
If you implement these best practices, your system will be a strong link in the security chain. As a result, the sensitive documents you have created are safe with you. However, now you have to send one to a consultant for review, so you email it as an attachment or share the file. The consultant may have weak security. He may access your data from a public computer in the hotel or Internet café, or he may be using public Wi-Fi in a coffee shop when he looks at your document.
The Encryption Myth
For thousands of years, encryption has been taught as the holy grail of privacy and security. With all the hype around encryption, most of us have forgotten that encryption is only as strong as the key that is used to encrypt and decrypt, and the security in communicating this key between the different trusted participants (key management). For more information on this subject, please read our Blog “Where are your encryption keys and who has control over them?”
Let’s look at the major categories of encryption solutions that currently dominate the market.
- Encryption provided by the cloud service providers. They encrypt your data at rest in the DB at the cloud service provider and claim that your data is safe since they encrypted it “For You!” In that model, your data is vulnerable to your cloud service provider, their employees, the government and anyone who can hack the cloud provider.
- Encryption provided by the many encryption vendors. These vendors are using keys that they control or are using your application password (email password) as a key for encryption. Hence, if your email credentials are hacked, the encryption will be useless (for more information, please read our Blog “How to validate your data encryption solution?”)
Remember: whoever has the keys can decrypt and examine your information any time they wish, and they can give the keys to third parties.
True Data Security in a Collaborative Environment
If you care about your data security in a complex collaborative chain, you have to make sure that you keep control of your data when you send it elsewhere. You never know what weak links your data have to go through to get to its destination, and you do not know how secure the destination is. If you can keep your information safe from the point of creation to the point of consumption and along the collaboration chain, these weak links do not matter.
One solution is to maintain security best practices that have been shown to reduce risk but to recognize that your sensitive information can still be compromised during transit through weak security links or on weak end-points. To address such weaknesses, you can implement a data-centric solution in which you retain control of your data at all times. The security of your data will no longer depend on the security measures of others. You keep control of your data, your security keys and who can read your files.
Such a solution masks your data as soon as it leaves your computer or mobile device, keystroke by keystroke or file by file. Nobody, not services providers, government agencies, unauthorized intruders or even your IT specialists can read what you have created. When a specific piece of information reaches someone who needs it, you can authorize that person to unmask the information on his computer or device. Everything else you control remains illegible. With such a solution, you can project a high level of security from your secure data environment through weak security links to the intended collaborators. Your onfidential information remains safe and under your control at all times.
For more information, please read “Mitigating the Risk of Data Breaches with Data Masking

With CloudMask, only your authorized parties can decrypt and see your data. Not hackers with your valid password, Not Cloud Providers, Not Government Agencies, and Not even CloudMask can see your protected data. Twenty-six government cybersecurity agencies around the world back these claims.
Watch our video and demo at www.vimeo.com/cloudmask
Share this article: