Since cybercrime is clearly not going away anytime soon, the business world must now deal with data security. Unfortunately, however, some corporations and associations still lack the strategies and support tools to protect themselves from cybercriminals and similar hacking groups. This means that organizations that take a strong-armed approach to data protection will have higher clout than others in their industries, as they become the most trusted by consumers and partners. Of course, merely presenting the fact that a firm practices exceptional cybersecurity isn't enough, especially in a business environment where data is the de facto standard of proof.
Enter security certifications. Businesses, associations and even individuals can become "certified" in specific cybersecurity practices and techniques or with processes and tools that typical organizations don't use. There are many certifications in this sector from a variety of different regulatory boards and international groups, and if businesses are certified in a certain category, they earn the right to flaunt that achievement in hopes of it attracting clients. But what does it really mean to have a security certification?
"A security certification means that an organization is following a third party's guidelines."
Does certified mean secure?
Generally speaking, a certification in a certain cybersecurity practice or infrastructure - whether it's compliance with the International Standards Organization's 27000 family of information security standards, strict adherence to the National Institute of Standards and Technology's framework or simply using a digital certificate for e-commerce transactions - means that an organization is following rules and guidelines (sometimes legally binding ones) put forth by a given association or agency. In other words, security certifications are proof that an entity meets a set of cybersecurity and data protection benchmarks defined by a third party.
At the end of the day, a security certification will do wonders for organizations that want to market their ability to protect sensitive data, but just because a business or association is certified in a cybersecurity standard or framework doesn't mean they have the absolute best security strategies and systems in place.
The CloudMask way
Organizations should always go above and beyond the bare minimums set forth by the associations that offer these security credentials. In many cases, this means having layers that protect each and every aspect of IT systems, but focusing primarily on securing data above anything else. After all, when all else fails, encryption services that obscure sensitive data - such as CloudMask - act as the last line of defense, protecting data even in the event of a breach. Sometimes encryption is required for a security certification, other times it isn't, yet regardless, it is absolutely essential.

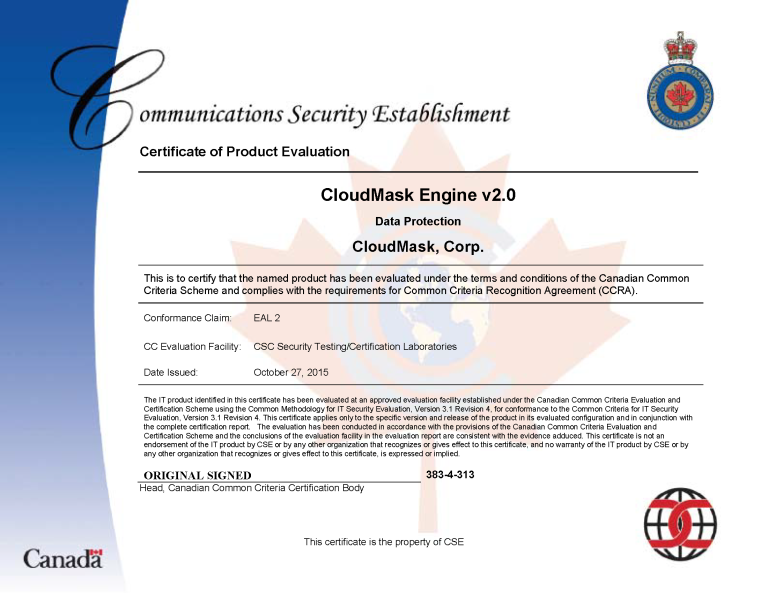
With CloudMask, only your authorized parties can decrypt and see your data. Not hackers with your valid password, Not Cloud Providers, Not Government Agencies, and Not even CloudMask can see your protected data. Twenty-six government cybersecurity agencies around the world back these claims.

Watch our video and demo at www.vimeo.com/cloudmask
Share this article: