Data security is one the most important aspects of digital business in today's IT ecosystem, as organizations continue to experience breach after breach. Unfortunately - like other technological solutions - enterprises, individuals and other entities are often confused by, uncertain of or misunderstand technobabble, system specifications and certificates. After all, the average consumers and business leaders have more things to worry about than learning all the lingo involved in the tech and cybersecurity spaces.
Regardless, at one point or another - hopefully sooner rather than later - organizations and individuals must choose and deploy a cybersecurity solution. Without insight into the minutia of this sector, these entities are likely lost when it comes to evaluating the authenticity and meaning behind security certifications.
This is part one of a two-part series that will explain how end users and businesses can identify and differentiate between cybersecurity solution certifications.
Two categories of certifications
Without further ado, let's discuss the differences between cybersecurity certifications by separating them into two categories: cryptographic engines and solution integrity. Some security products will have both of these elements, but it is important to understand what they mean by themselves.
"A certified cryptographic engine successfully protects data or systems from cyberthreats."
A cryptographic engine is the mechanism or component of a cybersecurity solution that leverages mathematical formulas to encrypt or otherwise obfuscate data. According to the National Institute of Standards and Technology, these modules are often parts of a product or application, providing all cryptographic services within that tool. Therefore, a certified cryptographic engine is a component that successfully protects data or systems from cyberthreats. An example would be FIPS-140 certification, as this indicates that the engine that encrypts data is more than capable of securing it.
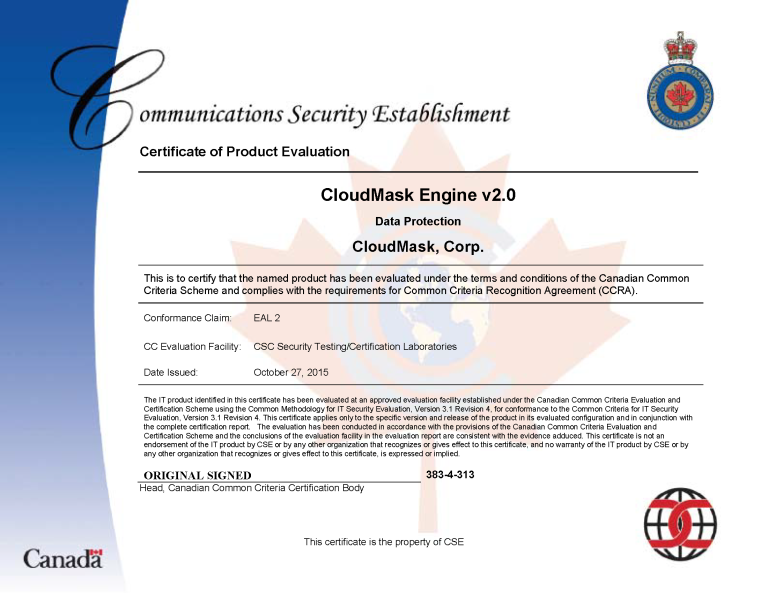
Solution integrity refers to a cybersecurity tool's ability to protect data or systems in an end-to-end manner. While cryptographic modules are identified as a single component, solution integrity certifications encompass entire solutions and typically handle data both before and after encryption, control key management, and detail or report events. These certifications are handled by accredited third-party institutes. One solution integrity certification, for example, is the Common Criteria for Information Technology Security Evaluation, which, simply put, ensures that cybersecurity software does what the solution vendor say it does.
The wildcard certificates
Apart from the two main types of cybersecurity certifications, there are special validations performed by government organizations and large industry firms - both of which ensure that vendors' claims regarding data protection are factual. For example, in the case of CloudMask, the federal government of Canada issued the company's cybersecurity solution a security certification. This acknowledged that not only are CloudMask's claims accurate, but its solution is welcome to operate on IT infrastructure that handled the highest level of confidential data.

With CloudMask, only your authorized parties can decrypt and see your data. Not hackers with your valid password, Not Cloud Providers, Not Government Agencies, and Not even CloudMask can see your protected data. Twenty-six government cybersecurity agencies around the world back these claims.
Watch our video and demo at www.vimeo.com/cloudmask
![]()