Cybersecurity and data breaches continue to make headlines as businesses and associations around the world fall victim to network intrusion and data theft. However, some organizations are still hesitant to just start spending thousands of dollars upgrading their security systems and improving data protection policies and practices. It isn't uncommon to hear someone asking, "Are investments into cybersecurity worth it compared to the cost of a data breach?"
Benjamin Dean, a fellow in the School of International and Public Affairs at Columbia University, told Fortune magazine that it's time to get down to the "hard evidence." He asserted that as long as businesses and associations have access to the facts, they can fix the cybersecurity problem. So, where is the evidence that current cybersecurity spending works?
The cost to protect
Businesses and associations are hesitant to publicly announce their cybersecurity spending habits. To add to the difficulties of tracking down the average investment in data protection, organizations have a variety of different needs when it comes to cybersecurity, since a health care provider might demand tighter security than a restaurant. However, the information security market is booming. According to Gartner, worldwide, organizations spent $81.6 billion in 2016 on information security, an increase of 7.9 percent from 2015.
"The average cost of losing sensitive information is approximately $4 billion."
The cost of a breach
There is no getting around the huge financial results of a data breach. According to Ponemon Institute's 2016 Cost of Data Breach Study, the average total cost of losing sensitive corporate or personal information is approximately $4 billion. Per stolen record, businesses and associations can spend anywhere between $145 and $158, with health card information costing the most to lose, at $355 per record.
The majority of data breach costs are associated with resolving the matter, as organizations must pay compliance fines and court fees, invest in forensic and investigation processes, and spend revenue on identity theft prevention services for customers or employees. Additionally, Ponemon's report noted that turnover of consumers directly impacts business costs, and from then on out, these organizations must spend more on customer acquisition as the reputational losses of a data breach last a long time.
The showdown
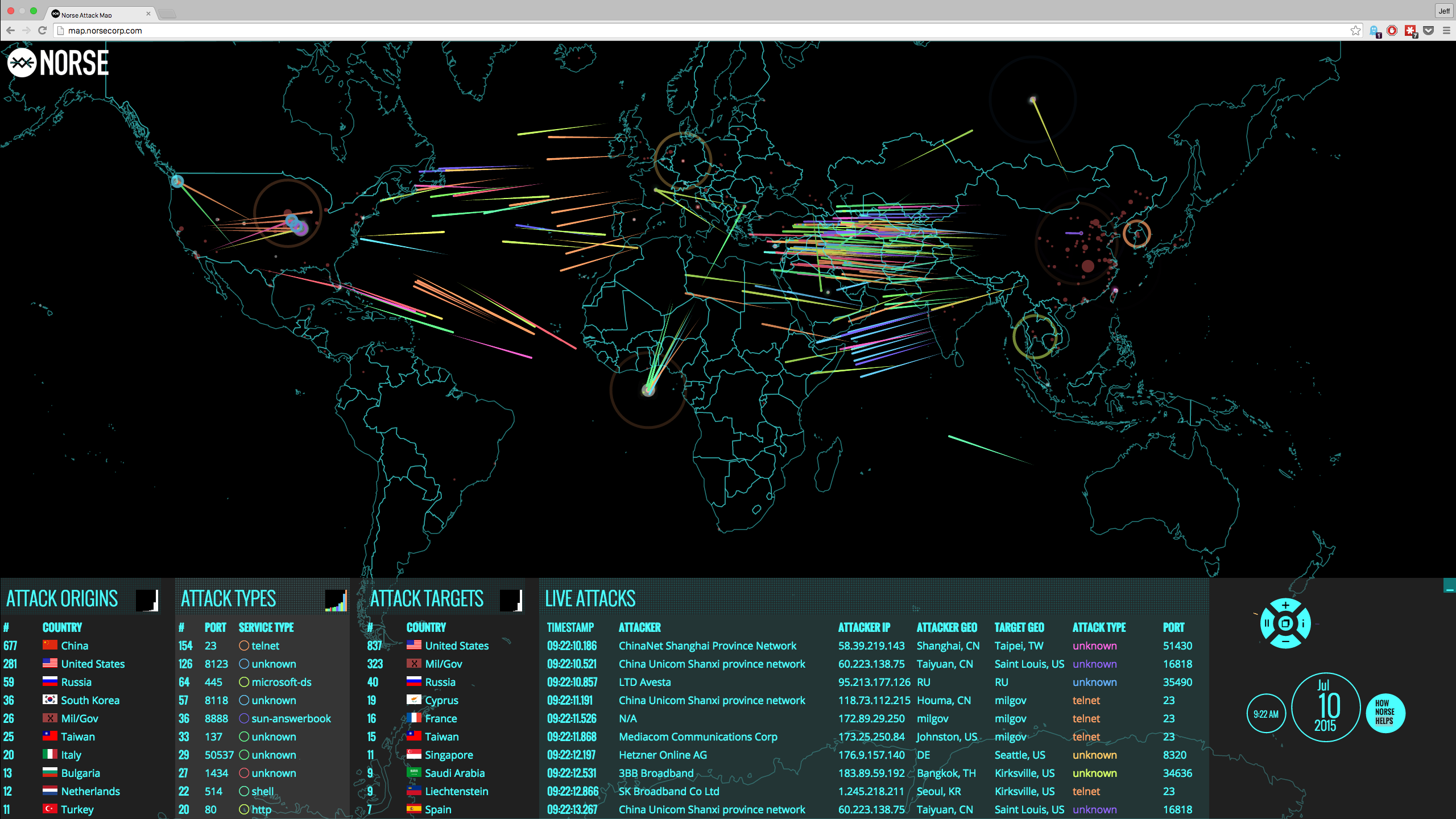
When Ponemon's data is paired with the Identity Theft Resource Center's statistics, it would appear that businesses and associations are spending too much on security that isn't working. With the average cost of a personal record coming in at $150 and 117,678,050 records accessed as of July 7 - according to ITRC - organizations have lost $17.65 billion six full months into 2015.
What is the solution?
Simply put, every organization needs a use case for cybersecurity solutions, otherwise the investment is made into a tool that doesn't work. With different monitoring software, physical firewalls and cutting-edge cybersecurity offerings, businesses and associations aren't successful at the only thing that matters: data protection.
CloudMask acts as the last line of defense when all the others fail, ensuring that even when breaches, data remains secure. In other words, cybercriminals cannot compromise information when organizations use CloudMask.It encrypts emails and cloud storage data, separates the key from the data and ensures that no one - not even CloudMask - can access or alter information.

With CloudMask, only your authorized parties can decrypt and see your data. Not hackers with your valid password, Not Cloud Providers, Not Government Agencies, and Not even CloudMask can see your protected data. Twenty-six government cybersecurity agencies around the world back these claims.
Watch our video and demo at www.vimeo.com/cloudmask
Share this article: