This article is the first of a series that explores data breach issues, threats to data security, compliance with regulations and effective solutions to reduce the risk of data breaches. In "What You Need to Know” we define key terms and provide an overview of the data security problems businesses are facing.
Data breaches are becoming more frequent while government agencies are tightening breach notification requirements. When your business suffers a data breach, you have to report the incidents to authorities and inform those whose data has been exposed know about the breach. Your business may also be fined and suffer legal complications. Costs resulting from data breaches are mounting, and the risks of not taking action are starting to threaten the ability of a business to continue normal operations. You either have to develop an action plan now or be forced to implement such a plan after a data breach that comes with high additional costs.
What is a Data Breach
Data breach is the unauthorized movement or disclosure of sensitive information to a party, inside or outside the organization, that is not authorized to have or see the information. Key features are the ability to see the data and the lack of authorization.
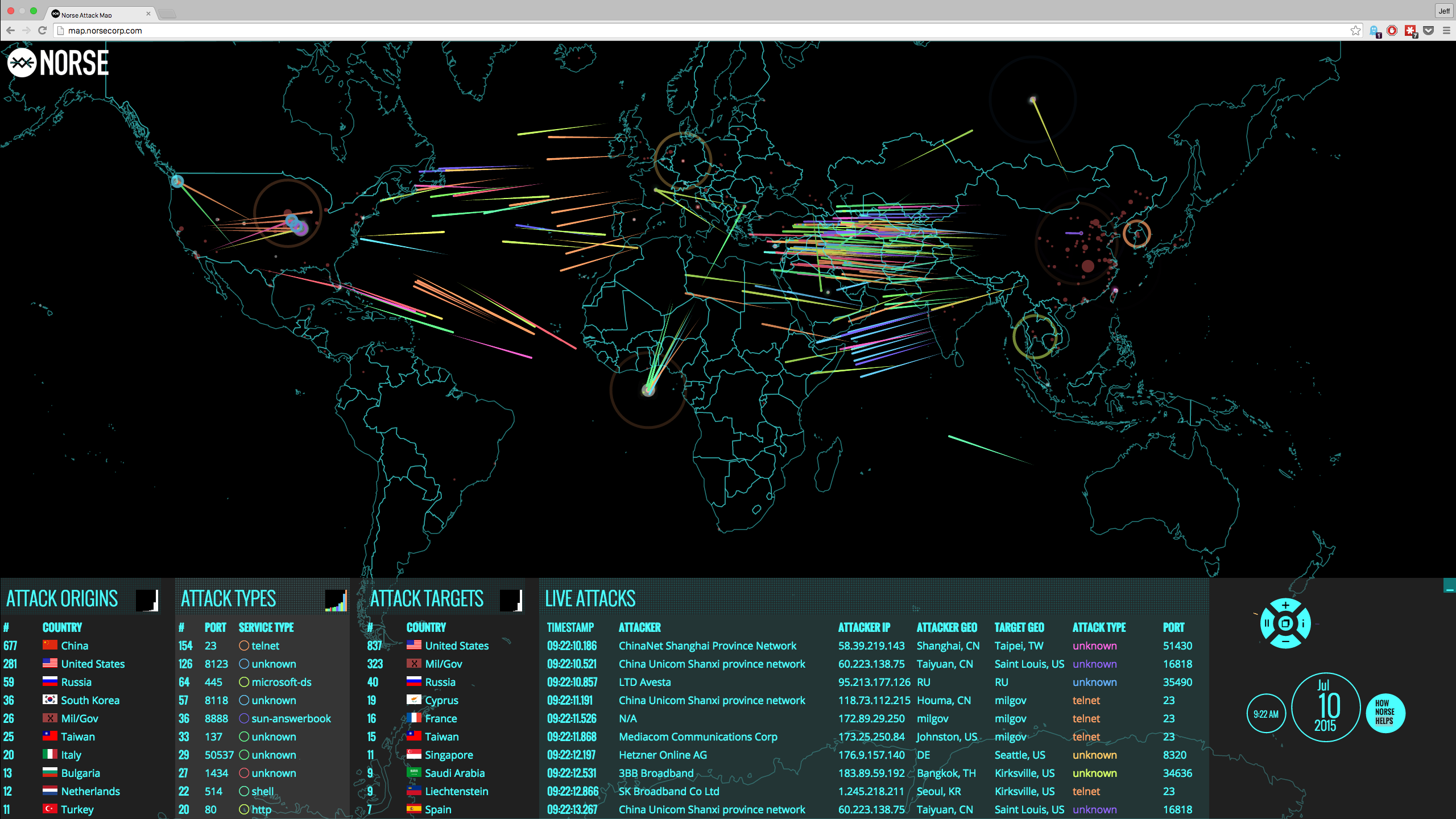
The traditional way is to prevent the attacker from accessing the data through hardened network perimeters through firewalls, security segmentation, creating a strong password and by using other techniques to protect the data location.
With the use of cloud computing and the increase in the complexity of the attacks, using only traditional perimeter protection to keep unauthorized individuals out is not enough. Every breach of your network will result in a data breach. For example, if you rely on usernames and passwords for access to your network, anyone who obtains a valid username and password can access your network and read your data. In that case, every unauthorized network access can result in a data breach.
To avoid data breaches, you need a second level of protection centered on protecting the sensitive data itself not accessing the data. A security failure giving access to data that can’t be read will not be considered a data breach. An action plan focused on protecting sensitive data so unauthorized individuals can't read it can provide adequate protection against non-compliance with data protection regulations.
Data Breach Costs and Regulatory Compliance
According to the National Conference of State Legislatures, almost all states now have data breach notification requirements. In Canada, they are part of the Digital Privacy Act. Many other countries internationally either have such laws or are considering them. Laws and regulations typically specify what constitutes a data breach, who has to be notified, what form the notifications have to take, what remedial action is required and what legal sanctions will apply. Costs for compliance can be substantial and can stretch out over an extended period.
Direct costs from notification requirements far exceed the costs of actually informing concerned parties of the breach. In addition to the cost of sending out the notifications, there are costs for customer support, compensation for damages and payment card replacement if financial data has been exposed and losing your reputation.
Indirect costs may include legal expenses to fight lawsuits such as class action cases brought by consumers, claims for damages by business partners who have notification costs due to your data breach and claims from investors. Fines and penalties may be high, and regulators may impose jail time for negligence.
With these tightening notification requirements and the increased costs of dealing with data breaches after they occur, you need a cost-effective way of reducing your risks. Businesses are looking for ways to avoid notification requirements by changing the way they store sensitive data. When private data remains secure even when a security failure allows unauthorized access to an IT system, then data breach laws and regulations may not be triggered.
Encryption and Safe Harbor
If your sensitive data is encrypted, a security failure exposing encrypted data may not be a data breach because the data is illegible. The Storage Network Industry Association explores how effective encryption as a safe harbor can help protect businesses from the costs of data breaches. Such effective encryption means that no private information is exposed when unauthorized individuals gain access to a network or an email account.
Safe Harbor encryption of data reduces the risk of incurring high costs due to data breach notification requirements in two ways. Firstly, some laws and regulations have language specifying that a company using effective encryption for its sensitive data is exempt from notification requirements for security breaches that expose this data. Secondly, if encrypted sensitive data is exposed, there is no damage, and no follow-up remedial actions to help the parties concerned is required. The key to employing this strategy is that the encryption has to be effective.
Conclusion
Faced with regulatory requirements and costs that could threaten your business, you have to take action to make sure the risks of data breaches on your IT systems are limited. Traditional perimeter security is no longer adequate to protect sensitive data. Data-centric protection using encryption can reduce your risks but only if the type of encryption used is effective.
In subsequent articles of this series, we’ll explore specific threats to both perimeter security and encrypted data and the issues that surface when you try to implement some forms of encryption. We will then build a case for a transparent, easy-to-use and cost-effective solution and how it can give you back complete control of your data, greatly reducing the risk of data breaches in your business.

With CloudMask, only your authorized parties can decrypt and see your data. Not hackers with your valid password, Not Cloud Providers, Not Government Agencies, and Not even CloudMask can see your protected data. Twenty-six government cybersecurity agencies around the world back these claims.
Watch our video and demo at www.vimeo.com/cloudmask
Share this article: