Businesses and consumers both invest time and money into securing private information, but too often, the focus is on preventing hackers from accessing data and therefore ensuring that sensitive information, trade secrets and personal data remain confidential. While data security certainly requires entities to protect data in that regard, there is a new threat to information and its integrity, and this aspect of data protection is frequently forgotten.
In September at a House Intelligence Committee hearing, National Security Agency director Michael Rogers explained the newest issue in cybersecurity: As attacks increase in sophistication and hackers become better at covertly accessing systems without authorization, cybercriminal groups and other organized threats are demonstrating the ability to manipulate digital data. According to The Hill, there haven't been many cyberattacks launched with the intent of compromising the integrity of data, but it is bound to happen, and it is possible that hackers have already altered data without anyone noticing.
"I definitely think that's something that will happen in the future," Jordan Berry, a threat intelligence analyst at FireEye, told The Hill.
"Data manipulation is the latest technique in the 'art of war in cyberspace."'
What is data manipulation
Referred to as data manipulation, the practice of altering digital documents and other information could mean disaster for corporations, health care providers, national security agencies and individuals around the world. In essence, hackers can infiltrate networks via any attack vector, find their way into databases and applications, and change information contained in those systems, rather than stealing data and holding it for ransom. Retired General and former National Security Agency Director Keith Alexander told FWC that data manipulation is the latest technique in the "art of war in cyberspace."
Why everyone should care
By just manipulating data instead of stealing it from under IT's noses, hackers could be more successful in these practices than if they stuck to data theft. With the abundance of breaches occurring on a regular basis, it is only a matter of time before organizations discover that their sensitive information and possible intellectual property has been significantly changed. Even worse, some cyberattacks could merely be reconnaissance missions, Alexander explained to FWC. Once inside systems, hackers can slowly collect data and analyze information, waiting for the perfect opportunity to strike.
Imagine this scenario: Cybercriminals steal intellectual property in a typical data breach, yet remain undiscovered on corporate networks for months. When the breached company goes to launch a product, it could find that all its data has been altered. Now, not only did hackers make off with trade secrets and product ideas, but they made it impossible for a business to recover the original documents.
Or, perhaps hackers break into a health care provider's network. Enterprise Tech contributor Todd Feinman described that scenario, emphasizing that data manipulation could take lives, if doctors read incorrect information and provide the wrong types of medicine or remedies.
Is data manipulation already occurring?
Feinman even posited that the Office of Personnel Management data breach from earlier in 2015 could have been a data manipulation attack. With access to millions of employee records, cybercriminal organizations could alter the integrity of information, adding unauthorized individuals to certain access lists or changing the identity and personal information of high-ranking officials in an attempt to frame them.
Meanwhile, The Hill explained how data manipulation has already affected the world's economy. In 2013, when Syrian cybercriminals hacked into The Associated Press' Twitter account and tweeted a fictitious news story, the Dow dropped 150 points, which caused market values to deflate by as much as $136 billion. Further attempts to spread misinformation are certainly possible, especially considering how sophisticated cybercrime has become.
Businesses could even be held responsible for data manipulation, even when they are the victim, Feinman told The Hill. After all, entities must protect their customer records and private information, and if they fail, fees, fines and lawsuits should be expected.
If you can't trust your own data, what can you trust?
The solution
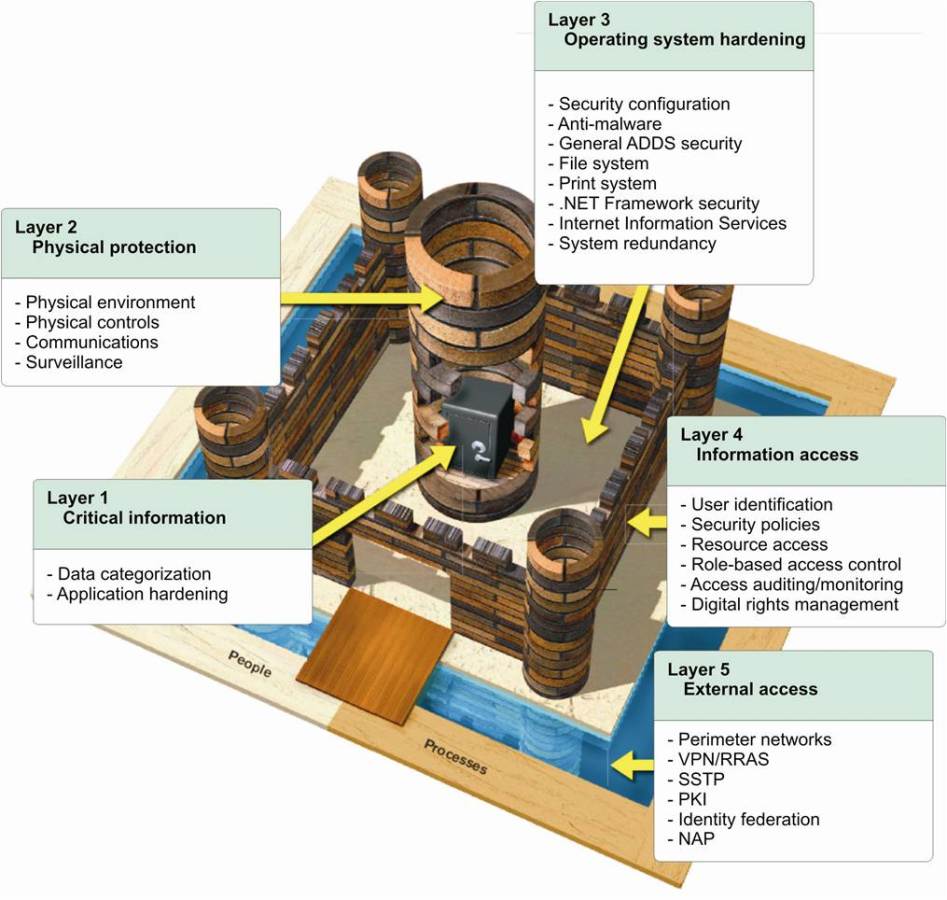
FCW reported that Cyber Command, a U.S. agency dedicated to preventing cybercrime under the U.S. Strategic Command, has set its sights on preventing data manipulation. But this government organization is likely to protect other federal associations and officials, not American businesses and consumers. Therefore, entities must find solutions that secure data and ensure its integrity at all times.
The increasing frequency of data breaches is forcing businesses to address data protection and cybersecurity issues to avoid substantial regulatory compliance costs.

With CloudMask, only your authorized parties can decrypt and see your data. Not hackers with your valid password, Not Cloud Providers, Not Government Agencies, and Not even CloudMask can see your protected data. Twenty-six government cybersecurity agencies around the world back these claims.
Watch our video and demo at www.vimeo.com/cloudmask
Share this article: