As cybercrime rapidly advances alongside the development of technologies in the business world, it is certain that hackers will target high-value organizations in an attempt to steal intellectual property, business strategies and other sensitive, mission-critical information. In fact, a recent article from the MIT Technology Review highlighted the discovery of cyberespionage details that relate to the defense and security sector, and all types of industries should heed this warning.
According to the source, some of the bigger firms, such as U.S. Steel, Alcoa, Allegheny Technologies and Westinghouse, were the victims of cyberespionage allegedly committed by hackers working for the China's People's Republic Army, Unit 613898. Simply put, if these organizations could be compromised, then other high-value targets are certainly vulnerable to cybercriminals and hacker groups that continue to launch attacks in an attempt to steal extremely sensitive business-critical and national security-dependent data. All sectors and industries must worry about advanced persistent threats as their current cybersecurity models are not capable of preventing APTs from compromising networks and data.
"An APT is 'an adversary that possesses sophisticated levels of expertise and significant resources.'"
What is the advanced persistent threat?
APTs might use some similar attack vectors as other cyberthreats, yet these are much more dangerous to businesses of all types and sizes - especially organizations in the defense and security industry, given the MIT Technology Review article. This is because APTs do as their name suggests and persistently try to infiltrate systems and databases owned by high-value targets.
According to the National Institute of Standards and Technology, an APT is "an adversary that possesses sophisticated levels of expertise and significant resources," and these individuals or groups of hackers will use their knowledge and their tools to attack organizations via multiple vectors. APTs ' goals vary, but in general, they try to steal information from entities with a blend of technological and social techniques.
"The advanced persistent threat: (i) pursues its objectives repeatedly over an extended period; (ii) adapts to defenders' efforts to resist it, and (iii) is determined to maintain the level of interaction needed to execute its objectives," the source read.
Rather than stealing data and selling it for money, APTs commit cybercrimes as an act of corporate or political espionage, and combined with their persistence; they form a dangerous threat to all organizations. They will target a particular high-value business, and not stop attacking until their goals are met. Many times, APT groups have access to zero-day exploits, making them even more severe of a problem.
'The Lockheed Martin Cyber Kill Chain'
As an example of the type of risk that APTs pose, one can look at modern security practices and how they hold up against these dangerous cyberthreats.
The Lockheed Martin Cyber Kill Chain, according to Lockheed Martin, is its "differentiator in the battle against [APTs]." The defense and aerospace firm takes advantage of "experienced analysts" that monitor cybercriminals ' activities and behavior, and then the company uses that information to build up defenses.
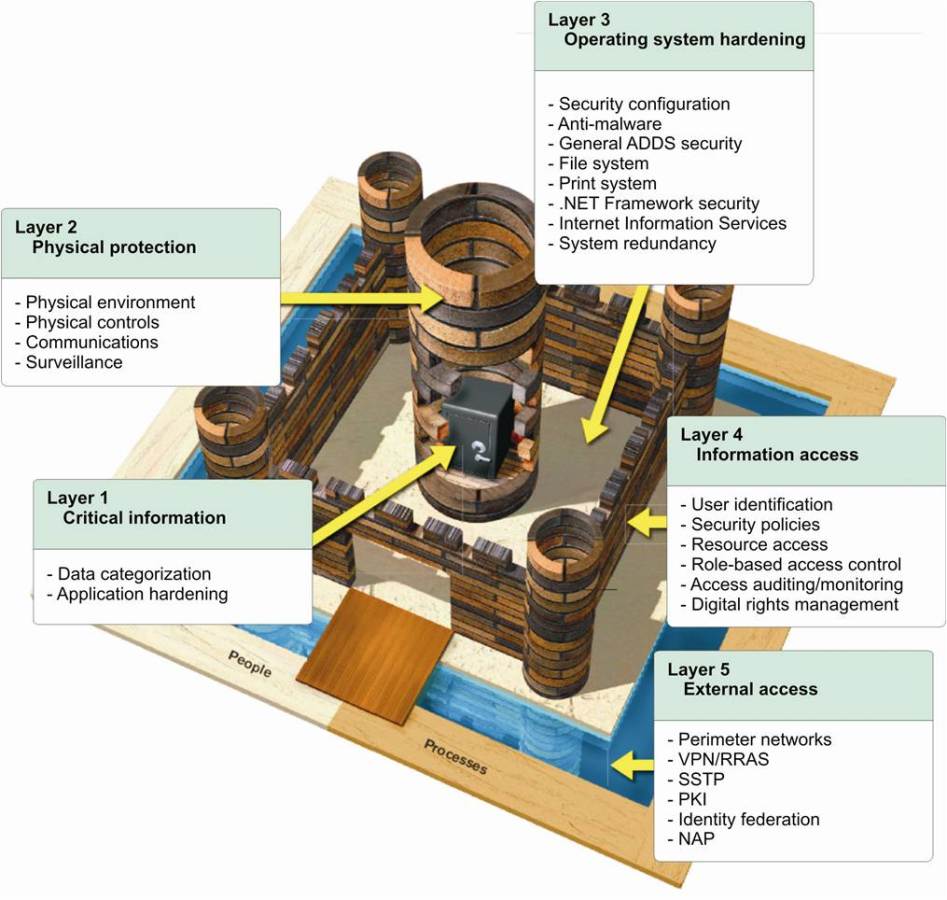
In brief, Lockheed Martin's APT cyberdefense strategy assumes that APTs will follow a known path to data when they attack, and their approach focuses on the perimeter and malware, rather than the zero-day exploits and other attack vectors that APTs typically leverage. Once firewalls and anti-virus tools are circumvented, hackers are inside networks and stealing data. Catching them after watching their behaviors (if you can watch!) means that it's too late, and instead, organizations should use multiple layers of data-centric protection and other traditional cybersecurity.
APTs could exist on corporate networks, and the organization could have no idea.
The solution
Using end-device data-centric protection running on user devices (such as CloudMask), transparently intercepts and analyzes data to identify and encrypt sensitive information from a variety of applications, such as Google, SalesForce, Box, Microsoft Office 365 and much more. This level of transparency ensures that neither users nor apps need to change their behaviors to be protected.
CloudMask converts sensitive data to tokens, which have the same structure as the original data, but they are meaningless, jumbled codes bearing no relation to the initial information. The tokens can not be broken through cryptoanalysis. As a result, the application receives meaningless tokens, instead of private, sensitive data. Accordingly, the application continues to function as before, and security is transparent, without requiring any changes to existing applications.
Data-centric protected by CloudMask will protect data even in the face of APTs because it assumes that hackers will breach defenses while ensuring that they will not be able to find any meaningful data. It is the last line of defense.

With CloudMask, only your authorized parties can decrypt and see your data. Not hackers with your valid password, Not Cloud Providers, Not Government Agencies, and Not even CloudMask can see your protected data. Twenty-six government cybersecurity agencies around the world back these claims.
Watch our video and demo at www.vimeo.com/cloudmask
![]()