What Is Wrong With Passwords-based data protection?
Today, Password-based data protection is the foundation of 99% of data protection. It’s ubiquitous: you want access to an account or information, so you type your username and password, and you can get in. For critical and restricted information, you might have to do it again, with a different password. Your company’s IT staff have set up the system so it works smoothly and you think your data is secure. But no matter how many times you are asked to identify yourself with a password, the pitfalls and risks to data protection remain. Passwords are not a secure way of protecting your data.
Hacking Passwords
One problem is that passwords are becoming less and less reliable. Lifehacker discusses how passwords offer less protection than in the past. That’s because hackers are getting better at guessing what they are. Powerful graphics processors can try millions of passwords in a short time, and most employees don’t know how to select a right password.
In fact, any password based on a word is not secure, even when you add a number or extra letters. A fast computer can try every word in a dictionary and then try them again with various letters and numbers added. Once hackers guess one of your passwords, they have a good chance at guessing the others, even if they are completely different. That’s because you probably followed some rule or method when setting up your passwords and the hacker can guess how you did it.
Completely random passwords are harder to guess but also difficult to create and remember. Passwords generated by computers are good, but nobody can remember several different passwords such as 3&Df7(k4#. The fact is that most people use insecure passwords, and you need additional data protection if you want to keep valuable information secure.
Even complex passwords are not as secure as you might think. Mandylion Research Labs states, “even if the password generated in accordance with the strong policy which incorporates the use of symbols and characters and numbers; even if it is changed regularly and not used concurrently elsewhere, your "strong" password is simply no contest for today's password-cracking tools.”
Hacking Password Storage
Hackers don’t spend a lot of time trying to guess the passwords of individuals because it takes considerable effort and the payoff is uncertain. Instead, they can get many user names and passwords at once by accessing servers where companies store the passwords of their customers and employees. It turns out that some companies don’t store this information very securely and that, when you are looking at a significant number of encrypted passwords, it can be relatively easy to break the code.
On the Sophos Naked Security Blog, Paul Ducklin writes about the Adobe data breach involving millions of usernames and passwords. He details how someone knowledgeable in encryption could guess a large number of the passwords even though they encrypted on the Adobe server. A lot of people use simple passwords such as “password,” “123456,” and “12345678.” When you guess these, the encryption gives you clues about how the rest of the passwords are encrypted. Adobe detected the data breach and reset all the passwords, but the incident clearly demonstrates the risks of relying exclusively on passwords for protection.
Weak Perimeters
The typical username and password combination is designed to protect a server, an account or a directory from unauthorized access. They act as barriers to define a secure perimeter and only people with a username and password can get inside. When passwords are not secure because they can be guessed or accessed on servers, the whole scheme breaks down. Once an unauthorized individual has your username and password, they can access all the data inside the secure perimeter, often from anywhere in the world.
SafeNet reports on the 2015 Data Security Confidence Index that describes how IT decision-makers have a high degree of confidence in their perimeter security while many of them have at the same time experienced data breaches and believe unauthorized users can access their networks. The index displays a disconnect between a perception of adequate security and an actual lack of protection. Part of the reason is that, when perimeter security fails, you can try and fix it, but your fix will make a tiny difference.
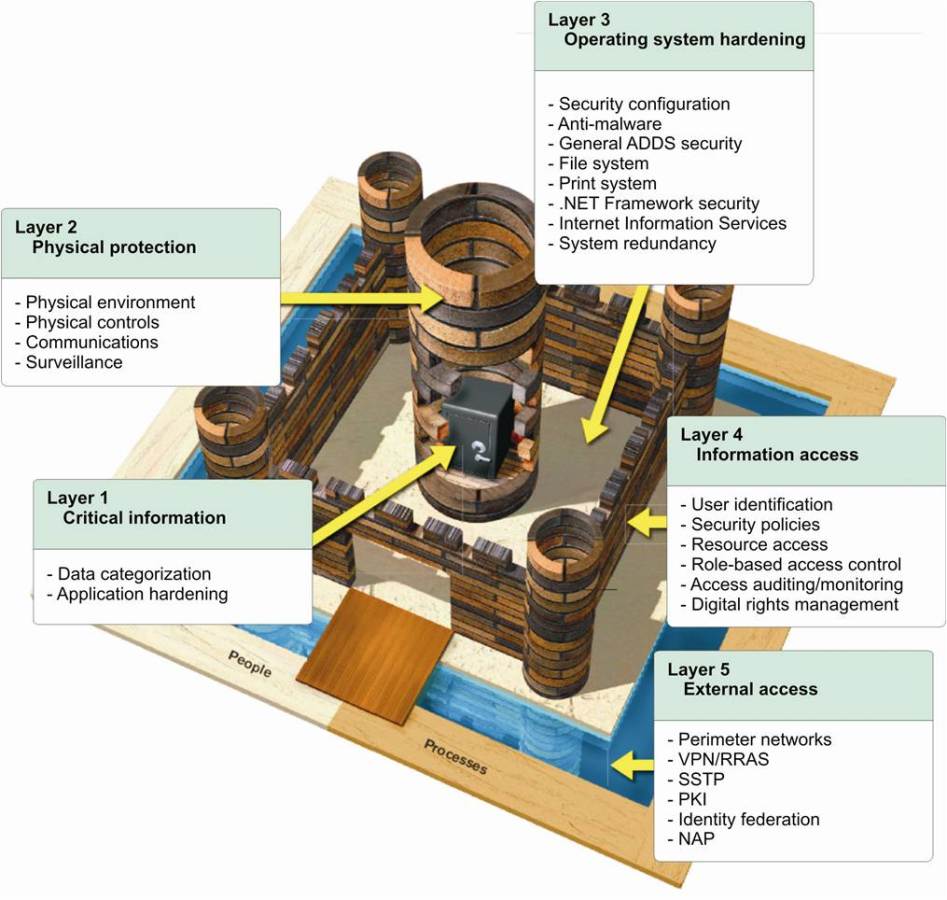
Perimeter protection can be made a strong as you like, by adding more secure perimeters and increasing the complexity of the usernames and passwords. You are trying to build impregnable walls with doors whose locks that are increasingly difficult to open. You can even start monitoring what goes through the doors and develop profiles for suspicious activity. The problem with such a strategy is two-fold.
First, you are making it more difficult for employees and customers to access the data they need. Increased perimeter security will not only slow down access and cause complaints. You will also need a large staff to deal with users who have lost or forgotten some of their complex log-in credentials or whose activity matches a suspicious profile. In the end, you have increased security overhead, unhappy customers, and lower productivity from employees.
Secondly, you are implementing additional layers of a strategy that have already shown weaknesses. Stronger perimeter security properly implemented may reduce risks, but the same weaknesses remain. Someone will guess a comparatively weak password or trick an employee into revealing it. Eventually, an unauthorized party will exploit such weaknesses, and a data breach will result.
You need additional data-centric protection to protect your data itself and not access to the data. This will prevent data leakage in case of breaches and allow you to manage your data securely at all times. Such protection has to be specific to the particular data set you are protecting. You can keep perimeter protection as general security, but you have to implement extra protection of valuable information. That way, when your perimeter protection fails, your sensitive data is still safe. Remember, “Breach is inevitable, data exposure is not”

With CloudMask, only your authorized parties can decrypt and see your data. Not hackers with your valid password, Not Cloud Providers, Not Government Agencies, and Not even CloudMask can see your protected data. Twenty-six government cybersecurity agencies around the world back these claims.
Watch our video and demo at www.vimeo.com/cloudmask
Share this article: