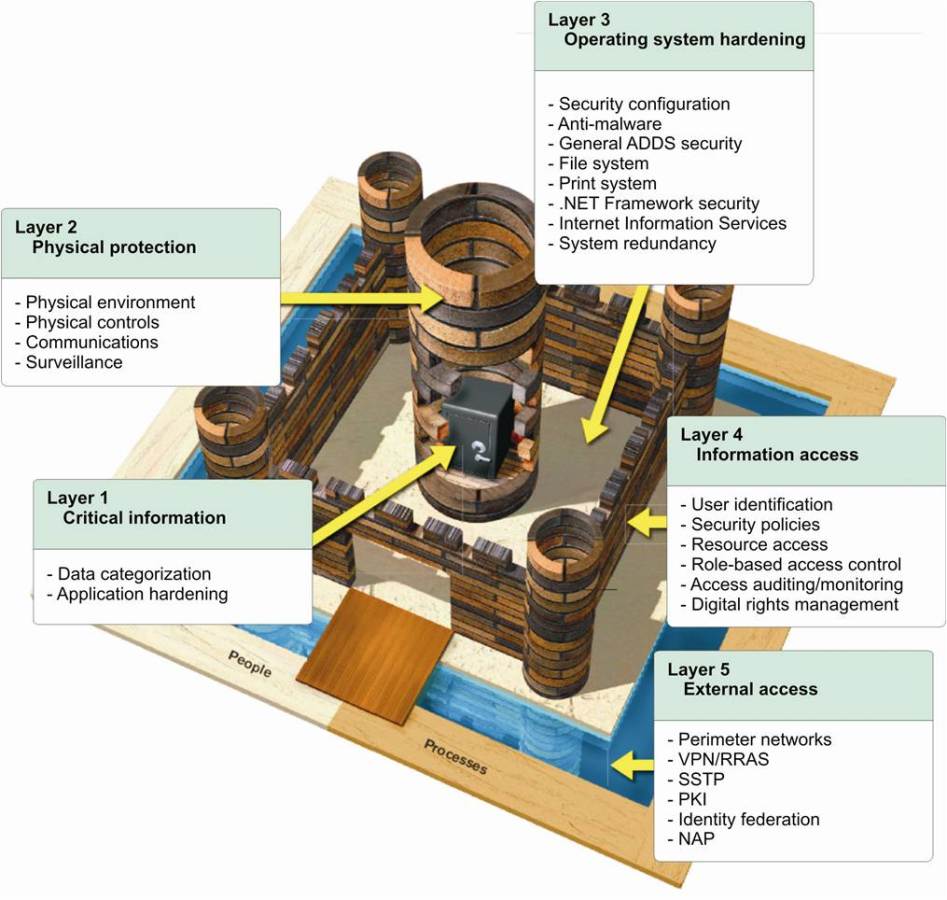
 Data protection issues have come center stage as organizations move from legacy applications to those that store and manipulate data in a hybrid environment. Previously, IT security specialists sought to protect the boundaries of their networks and provide reliable perimeter security. Anything inside the perimeter was trusted and what was outside was not. This mindset led to the development of secure firewalls, tight access control mechanisms, intrusion detection and prevention, and tools that minimized the possibility of reaching/accessing company data as the main technique of data protection.
Data protection issues have come center stage as organizations move from legacy applications to those that store and manipulate data in a hybrid environment. Previously, IT security specialists sought to protect the boundaries of their networks and provide reliable perimeter security. Anything inside the perimeter was trusted and what was outside was not. This mindset led to the development of secure firewalls, tight access control mechanisms, intrusion detection and prevention, and tools that minimized the possibility of reaching/accessing company data as the main technique of data protection.Fundamentally, IT security specialists were focused on the protection they could provide their network assets (server, routers, etc.), this was both logically as well as physically, a Network-centric approach. Even though this approach could be shown to have weaknesses in that it had limited protection against insider attacks, it did provide effective security against external attackers.
Times have changed. Our data is no longer confined to our network or our server farm that it can be protected by implementing strong perimeter protection. We live in a hybrid world. Some critical data could be stored on premises while some could be stored outside the company premises in the cloud. Data processing could occur on company servers or the cloud provider’s servers. Instances of such hybrid forms of storage and processing will only increase in the future. In such an environment, it is no longer enough to rely on perimeter security alone. Businesses need to use a protection mechanism that stays with their data throughout its lifecycle from creation, movement, processing, rest and consumption; this is a data-centric approach rather than a network-centric approach.
Since data under process is part of the data lifecycle, any successful security mechanism must ensure that the applications which use the data being protected continue to function correctly regardless of whether the security system is in place or not.
There are many other issues influencing Data Protection. While all data is to be kept secure, you may want some types of data to be accessible by a large number of users. Other data may need to be handled by a smaller group. Essentially, Data Protection professionals need to strike a balance between strong security, ease of use and providing appropriate levels of control over data.
Any data protection scheme is an important part of a comprehensive security policy that takes into considerations the following imperatives
Any data protection scheme is an important part of a comprehensive security policy that takes into considerations the following imperatives
- The type of data which is to be protected and its security level
- What are the issues – both legal and corporate – that must be met and complied with
- A list of users who have rights to access each data type and a clear definition of the rights of everyone that access the data.
In many cases, the answers to these questions become simpler if one understands the reason why particular data is to be protected. For example, in protecting personal information, if the details of the individual (name, address, birthdate, etc.) concerned are encrypted then the person’s Social Insurance Number is simply a string of numbers that does not reveal any personal information. This implies that by protecting certain key elements of data, we can often avoid the need to protect other elements of related data to protect critical personal information.
CloudMask provides proven and comprehensive solutions for data protection in hybrid environments for different applications. These solutions allow organizations to
- Be aware of the state of the art in implementing Data Protection in hybrid environments while providing complete functionality for their existing applications
- Guard their data throughout its lifecycle irrespective of the application or the physical location to ensure that it stays secure from unauthorized access
- Examine user activity and how data is used and create patterns to detect abnormal use.

With CloudMask, only your authorized parties can decrypt and see your data. Not hackers with your valid password, Not Cloud Providers, Not Government Agencies, and Not even CloudMask can see your protected data. Twenty-six government cybersecurity agencies around the world back these claims.
Watch our video and demo at www.vimeo.com/cloudmask
![]()