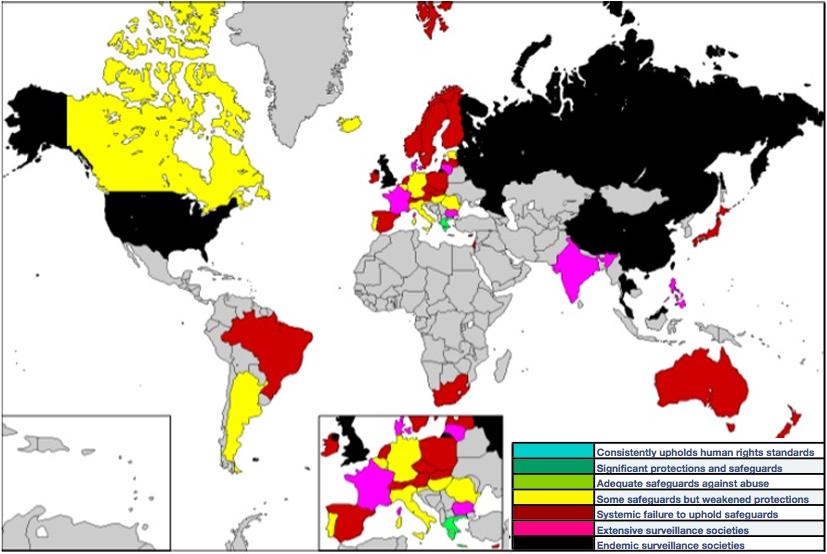
This is the third part of 5 parts discussion where I will present the main risks of Cloud Computing and how CloudMask addresses those risks. I hope to receive your comments. W.A. Governments around the world have Digital Surveillance Programs that can be used to demand legal access to your data stored with a Cloud Service Provider (CSP) or Telecommunication companies....
This is the second part of 5 parts discussion where I will present the main risks of Cloud Computing and how CloudMask addresses those risks. I hope to receive your comments. W.A. Any organization that is contemplating using cloud-based services for its computing architecture is necessarily worried about how it is to protect, control and ensure safety for its data...
Common sense security says it’s no secret that when we go online, we take the risks of entering a war-zone. Cyberspace remains a domain of commerce in which rule of law is still emerging. As it relates to physical property, movement across the seas, or navigating in the skies, the law is well established, defined and enforced. But law and its enforcement in cyberspace...
If you look around, you will find hundreds of examples of data security being breached. Even large and well-established organizations with highly skilled and qualified staff and multiple layers of security are not safe. One just has to look at breaches at TJX Companies (94 million credit card details lost). Heartland Payment Systems (134 million credit cards exposed), RSA...
Cloud computing is providing substantial cost savings and scale benefits to most organization’s IM/IT resources, however, the area of benefits associated with cloud computing and its ability to enable collaboration, is often overlooked and underplayed. Cloud provides a significant competitive advantage for inter‐organizational collaboration. Specifically, this is...
Law firms need to balance compliance with the cloud in an age when both are critical to success. The cloud has become a fundamental part of business, and thanks to the cost-efficiency, scalability, and agility that these systems and services offer, it won't be going away anytime soon. From storage to computing, every organization in a variety of sectors has empowered...
October 21, 2014
Leave a comment
Data Sovereignty,
Compliance,
Breach,
Legal,
Data Masking
By CloudMask Team