The Common Criteria for Information Technology Security Evaluation (CC) is an international standard (ISO/IEC 15408) for computer security certification.
Common
In other words, Common Criteria provides assurance that the process of specification, implementation and evaluation of a computer security product has been conducted in a rigorous and standard and repeatable manner at a level that is commensurate with the target environment for use.
The Participants in this Arrangement share the following objectives:
The CC is the driving force for the widest available mutual recognition of secure IT products.
Common Criteria is used as the basis for a Government

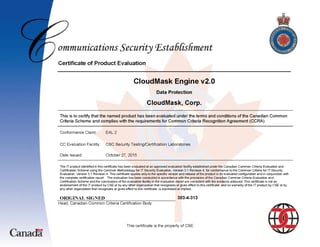
The Communications Security Establishment (CSE), is the Canadian government's national cryptologic agency. It is responsible for foreign signals intelligence (SIGINT) and protecting Canadian government electronic information and communication networks. CSE certified CloudMask Engine; a software application that enables users to protect their sensitive data while leveraging public and/or private cloud applications. CloudMask works transparently by intercepting application data before it is transmitted to the cloud and replaces it with a random token representing the data in a process called tokenization. The tokenized data, referred to as a “mask”, is transmitted to the cloud application and is meaningless unless viewed by an authorized CloudMask user.
This evaluation was carried out in accordance with the rules of the Canadian Common Criteria Evaluation and Certification Scheme (CCS). The scope of the evaluation is defined by the security target, which identifies assumptions made during the evaluation, the intended environment for CloudMask Engine, and the security functional/assurance requirements.
Communications Security Establishment, as the CCS Certification Body, declares that the CloudMask Engine evaluation meets all the conditions of the Arrangement on the Recognition of Common Criteria Certificates.